CI/CD Pipeline Security and Software Supply Chain Attack Prevention
InvisiRisk: The Build Application Firewall (BAF)
InvisiRisk watches your builds as they happen, and stops threats before they ship. It’s not a pre-build or post-build scanner. It’s a real-time firewall for your CI/CD pipelines.

Inline Protection
Monitor live build activity
Apply policies in real time
Halt builds on critical violations
What Is a Build Application Firewall (BAF)?
Just as a Web Application Firewall (WAF) is designed to protect web servers, a Build Application Firewall (BAF) is purpose-built to protect CI/CD pipelines and build systems. A BAF understands the protocols and communications patterns used within build environments, enabling real-time validation and enforcement of security policies.
Operating as a real-time broker for CI/CD communication, a BAF can enforce policy over build-time behavior such as network access, dependency retrieval, secrets usage, and artifact creation. This helps prevent tampering, data exfiltration, and malicious code injection while also providing evidence for policy compliance.
Monitor live build activity. Halt builds on critical violations
Monitor the build process, providing on-the-fly validation of components as they are pulled in. Policies are applied to issue warnings or stop the build for the most serious policy violations. The application of policy during the build ensures compliance with regulations related to data and customers safety.

Get Comprehensive
Recognize all build components, including transitive dependencies and rogue artifacts.
Stay Engaged
Track build systems and updates across GitHub, GitLab, Jenkins, and Azure DevOps.
Automate Enforcement
Enforce IP traffic rules using Open Policy Agent (OPA) and Rego-based policies.
Automate Action
Stop builds for major policy breaches like secrets exfiltration, typo-squatting, or unauthorized downloads.
Be Everywhere
Deploy in cloud or on-prem environments with protocol-aware inspection.

Trust, but Verify
Prevent or alert on risky downloads from unknown or blacklisted sources.
What does InvisiRisk catch that existing scanners and agents miss?
InvisiRisk inspects and enforces policies across all CI/CD traffic to stop unexpected transactions during build time.
Supports custom rules
Blacklists/Whitelists
Enterprise-wide policy enforcement for secret leaks and much more

Stops data exfiltration in real-time (even for zero-day attacks)

Blocks unwanted changes (such as repository permission changes)

Blacklists/Whitelists for allowed network traffic

Quarantines (blocks or warns on) packages with recent changes
Stay in the loop
Be the first to know about our latest product updates and company news.
No spam. Just the good stuff! We also respect your privacy and keep your info safe.
Build Application Firewall & InvisiRisk FAQs
Find answers to common questions about InvisiRisk, Build Application Firewall technology, and CI/CD pipeline security. This FAQ explains how InvisiRisk protects build systems, supports GitHub Actions and self-hosted runners, helps reduce software supply chain risk, and fits into modern DevSecOps programs.
Frequently asked questions
What Is a Build Application Firewall (BAF)?
Just as a Web Application Firewall (WAF) is designed to protect web servers, a Build Application Firewall (BAF) is purpose-built to protect CI/CD pipelines and build systems. A BAF understands the protocols and communications patterns used within build environments, enabling real-time validation and enforcement of security policies.
Operating as a real-time broker for CI/CD communication, a BAF can enforce policy over build-time behavior such as network access, dependency retrieval, secrets usage, and artifact creation. This helps prevent tampering, data exfiltration, and malicious code injection while also providing evidence for policy compliance.
Why Does CI/CD Need Its Own Firewall?
CI/CD pipelines are highly privileged environments. They often access source code, secrets, signing keys, package registries, and external services with broad permissions.
Modern threats and zero-day attacks have shown that traditional firewalls and runtime security tools do not adequately protect build systems. A dedicated build firewall helps ensure that builds perform only approved actions while they run, reducing software supply chain risk at one of its most vulnerable stages.
How is a Build Application Firewall different from existing CI/CD security tools?
Most CI/CD security tools analyze code, dependencies, or artifacts and report potential risks. Tools such as SAST, SCA, and container scanners identify known vulnerabilities, misconfigurations, or license issues, typically before or after the build.
A Build Application Firewall protects the build while it is running. Instead of only analyzing code or artifacts, InvisiRisk monitors and enforces security policy on real-time build behavior, including network access, dependency retrieval, secrets usage, and artifact publication.
This allows InvisiRisk to stop attacks that traditional scanners may miss, such as malicious dependencies attempting data exfiltration, unauthorized outbound connections, or tampering with build outputs. In this way, a BAF complements existing DevSecOps tools by adding a real-time enforcement layer to the CI/CD pipeline.
How is a Build Application Firewall different from a Web Application Firewall?
A Web Application Firewall protects applications at runtime by filtering inbound HTTP traffic. It is designed to understand web application traffic and enforce policy for web-facing systems.
A Build Application Firewall is designed for build environments rather than production web traffic. It focuses on build-time behavior such as outbound connections, dependency resolution, secrets access, and artifact creation. Those controls fall outside the normal scope of a WAF.
Why is build-time security critical for software supply chain protection?
Build time is when source code becomes a deployable artifact. Any compromise introduced at this stage can be propagated downstream to internal environments, partners, or customers.
Build systems are also high-value targets because they often have privileged access to source code, secrets, signing keys, package registries, and external services. Build-time security helps ensure that only approved dependencies, expected behaviors, and authorized outputs are included in released software.
Can a Build Application Firewall help secure open-source dependencies?
Yes. Modern supply chain attacks can involve malicious or backdoored packages, dependency confusion, or packages with known exploited vulnerabilities.
InvisiRisk enforces policies around which dependencies can be retrieved, from where, and under what conditions. By controlling dependency retrieval during execution, it helps reduce the risk of malware, unauthorized packages, or unexpected components being introduced into the build.
How does InvisiRisk function during a build?
The InvisiRisk Build Application Firewall acts as a network-level proxy that brokers CI/CD communication. It inserts policy enforcement directly into the build execution path and observes build activity in real time.
It applies guardrails around outbound network access, dependency retrieval, secrets usage, and artifact creation and publication. If a build attempts an action outside policy, that action can be blocked, logged, or escalated automatically.
How does InvisiRisk prevent secrets exfiltration during builds?
InvisiRisk monitors and controls build-time access to secrets and outbound connections. By analyzing outbound traffic from the build system, it can detect attempts to exfiltrate secrets in real time.
Through strict egress and usage policies, InvisiRisk helps prevent secrets from being transmitted to unauthorized destinations, even if malicious code is introduced into the build.
How does InvisiRisk stop unauthorized external connections?
InvisiRisk enforces allowlist-based network policies for build processes. Builds can connect only to approved services, repositories, and endpoints.
Unexpected or unauthorized outbound connections can be blocked in real time, reducing the risk of data exfiltration or command-and-control callbacks.
How does InvisiRisk detect rogue or unexpected artifacts?
InvisiRisk validates build outputs against defined expectations.
If a build attempts to generate, modify, or publish artifacts outside policy, such as altered binaries, unexpected files, or dependencies governed by restrictive license policies, the build can be flagged or halted before those outputs move downstream.
How does InvisiRisk relate to SBOM accuracy?
Because InvisiRisk observes actual build-time network traffic, it has visibility into the true provenance of packages and dependencies used during the build.
After the build, organizations can use that observed data to support more accurate artifact records and software bill of materials generation. Compared with approaches that look only at manifests or logs, build-time observation gives teams stronger evidence of what was actually retrieved and used.
Does InvisiRisk slow down CI/CD pipelines?
InvisiRisk operates inline with minimal performance impact. Policies are enforced during execution without requiring extra build stages or manual reviews.
In typical cases, this adds only seconds to build-time execution, helping teams improve security without significantly affecting developer velocity.
Which CI/CD platforms does InvisiRisk support?
InvisiRisk is designed to work with modern CI/CD platforms and build systems used in enterprise environments. It operates inline with the build process and is intended to be platform-agnostic, protecting builds regardless of the orchestrator or cloud provider.
InvisiRisk currently offers out-of-the-box integration with GitHub Actions, Jenkins, Bitbucket Pipelines, and Azure Pipelines. Additional platforms such as TeamCity, GitLab, AWS CodeBuild, and CircleCI can be supported through custom onboarding, based on the current draft.
How quickly can InvisiRisk be deployed?
Many organizations deploy InvisiRisk in hours or days (depending on environment and approvals). Because it operates as a network-level proxy, it typically requires only limited changes to existing CI/CD pipelines.
Most teams begin in monitoring mode and enable enforcement after policies have been validated. For teams using GitHub Actions with relatively straightforward pipeline configurations, the InvisiRisk GitHub App can accelerate onboarding by analyzing workflow YAML and proposing the necessary changes through a pull request. The only manual step is typically adding the InvisiRisk API key to the repository secrets.
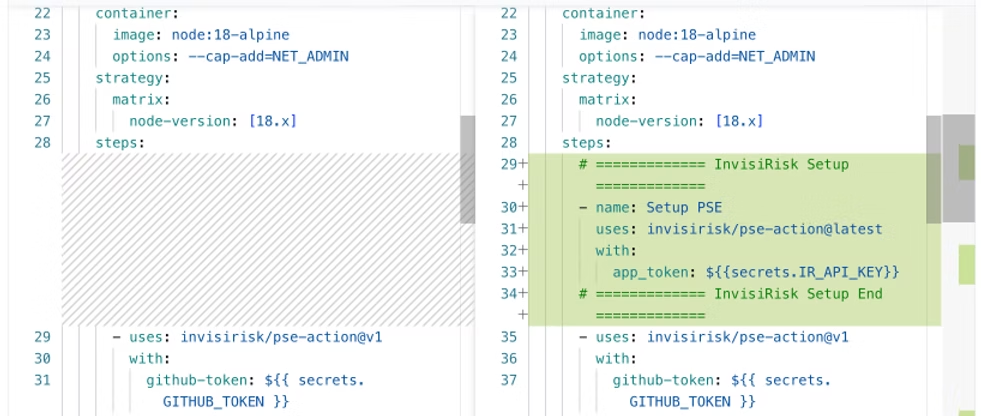
What changes does InvisiRisk make to a GitHub Actions workflow?
When installed as a GitHub App, InvisiRisk analyzes the repository’s existing GitHub Actions workflow and proposes a small set of changes required to route build traffic through the InvisiRisk Build Application Firewall.
These changes typically include enabling policy enforcement during the build and ensuring the build environment can communicate with the InvisiRisk service. The updated workflow YAML is generated automatically, and the app opens a pull request so teams can review the exact changes before merging.
The only manual configuration typically required is adding the InvisiRisk API key to GitHub Secrets.
Does InvisiRisk work with self-hosted runners?
Yes. InvisiRisk works with both GitHub-hosted and self-hosted runners.
For self-hosted runners, the main requirement is that the runner environment routes build traffic through the InvisiRisk proxy so policy enforcement and monitoring can occur during build execution. This allows organizations to retain their existing runner infrastructure while adding build-time security controls.
Does InvisiRisk require changes to developer workflows?
No. Developers continue using their existing tools and pipelines. InvisiRisk operates during the build process and enforces security policy without requiring changes to application code.
Where does InvisiRisk sit within the DevSecOps security stack?
InvisiRisk runs inline with the build process, between source retrieval and artifact publication. It complements existing tools such as Static Application Security Testing (SAST), Software Composition Analysis (SCA), container scanners, and runtime protections by adding real-time controls during build execution.
Rather than replacing the rest of the DevSecOps stack, InvisiRisk is best understood as an additional layer focused on build-time behavior and enforcement.
How does InvisiRisk support zero-trust principles in CI/CD
InvisiRisk applies zero-trust principles to build systems by validating build-time actions such as network access, dependency retrieval, secrets usage, and artifact publication.
Instead of assuming the build environment is trustworthy by default, InvisiRisk continuously verifies that activity remains within approved policy.
Can teams customize enforcement thresholds?
Yes. InvisiRisk policies are configurable and can operate in monitoring, alerting, or blocking modes.
This allows teams to align enforcement levels with their risk tolerance and security maturity. That “monitor first, then enforce” progression also matches language you’ve been using elsewhere in the content.
How are policy violations reported?
Policy violations can be surfaced through build-time events, logs, and optional email alerts.
Teams can see what policy was violated, when it occurred, and what action was taken. This helps support faster investigation and remediation.
What happens when InvisiRisk halts a build?
If a violation triggers enforcement, the build is stopped before compromised or unauthorized artifacts are produced or promoted.
Teams receive immediate feedback so the issue can be investigated and corrected quickly.
Does InvisiRisk create an audit trail for every build?
Yes. InvisiRisk creates a detailed audit trail for each protected build, including enforced policies, observed behavior, and outcomes.
This audit trail can support compliance reporting, incident analysis, and broader security assurance activities.
Is a Build Application Firewall relevant for regulated industries?
Yes. Regulated industries often need demonstrable control over how software is built and released.
InvisiRisk supports that need through enforceable policies, detailed auditability, and stronger control over build-time behavior. The draft also ties this to SBOM-related evidence and compliance review support.
Can InvisiRisk help with compliance framework?
Yes. InvisiRisk provides audit trails and enforcement controls that can support compliance requirements across frameworks such as SOC 2, ISO 27001, and emerging software supply chain standards.
Who Uses InvisiRisk
InvisiRisk is typically used by DevOps teams responsible for CI/CD infrastructure, DevSecOps teams responsible for securing development operations, application security teams, and platform engineering teams.
It provides centralized visibility and control over build behavior without requiring developers to change how they write code.
